최근 Blackhat 2018 USA / Defcon 행사가 진행됬었습니다. 자료도 슬슬 올라오고 어떤 내용의 발표들이 있었는지 Title만 정리해둡니다. (천천히 읽어봐야겠네요, 재미있는건 포스팅하도록 하겠습니다)
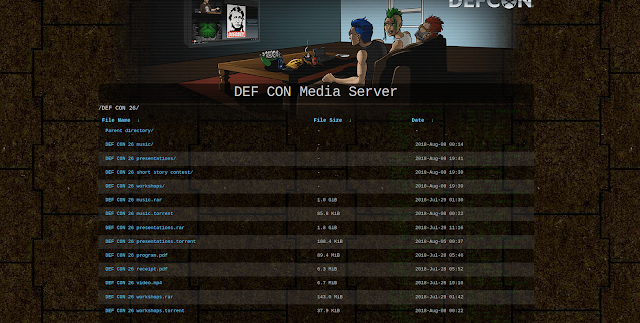
자료는 모두 media 서버로 올라와있습니다. https://media.defcon.org/DEF%20CON%2026
Briefings
| - | Optimistic Dissatisfaction with the Status Quo: Steps We Must Take to Improve Security in Complex Landscapes |
|---|---|
| - | A Brief History of Mitigation: The Path to EL1 in iOS 11 |
| - | A Deep Dive into macOS MDM (and How it can be Compromised) |
| - | A Dive in to Hyper-V Architecture & Vulnerabilities |
| - | A Tangled Curl: Attacks on the Curl-P Hash Function Leading to Signature Forgeries in the IOTA Signature Scheme |
| - | AFL's Blindspot and How to Resist AFL Fuzzing for Arbitrary ELF Binaries |
| - | AI & ML in Cyber Security - Why Algorithms are Dangerous |
| - | An Attacker Looks at Docker: Approaching Multi-Container Applications |
| - | Another Flip in the Row |
| - | Applied Self-Driving Car Security |
| - | Are You Trading Stocks Securely? Exposing Security Flaws in Trading Technologies |
| - | ARTist - A Novel Instrumentation Framework for Reversing and Analyzing Android Apps and the Middleware |
| - | Automated Discovery of Deserialization Gadget Chains |
| - | Back to the Future: A Radical Insecure Design of KVM on ARM |
| - | Beating the Blockchain by Mapping Out Decentralized Namecoin and Emercoin Infrastructure |
| - | Behind the Speculative Curtain: The True Story of Fighting Meltdown and Spectre |
| - | Black Box is Dead. Long Live Black Box! |
| - | Blockchain Autopsies - Analyzing Ethereum Smart Contract Deaths |
| - | Breaking Parser Logic: Take Your Path Normalization off and Pop 0days Out! |
| - | Breaking the IIoT: Hacking industrial Control Gateways |
| - | CANCELLED: Too Soft[ware Defined] Networks: SD-WAN VulnerabilityAssessment |
| - | Catch me Yes we can! – Pwning Social Engineers using Natural Language Processing Techniques in Real-Time |
| - | Compression Oracle Attacks on VPN Networks |
| - | Decompiler Internals: Microcode |
| - | Deep Dive into an ICS Firewall Looking for the Fire Hole |
| - | Deep Neural Networks for Hackers: Methods Applications and Open Source Tools |
| - | DeepLocker - Concealing Targeted Attacks with AI Locksmithing |
| - | Demystifying PTSD in the Cybersecurity Environment |
| - | Detecting Credential Compromise in AWS |
| - | Detecting Malicious Cloud Account Behavior: A Look at the New Native Platform Capabilities |
| - | Dissecting Non-Malicious Artifacts: One IP at a Time |
| - | Don't @ Me: Hunting Twitter Bots at Scale |
| - | Edge Side Include Injection: Abusing Caching Servers into SSRF and Transparent Session Hijacking |
| - | Efail: Breaking S/MIME and OpenPGP Email Encryption using Exfiltration Channels |
| - | Every ROSE has its Thorn: The Dark Art of Remote Online Social Engineering |
| - | Exploitation of a Modern Smartphone Baseband |
| - | Exposing the Bait: A Qualitative Look at the Impact of Autonomous Peer Communication to Enhance Organizational Phishing Detection |
| - | Finding Xori: Malware Analysis Triage with Automated Disassembly |
| - | Fire & Ice: Making and Breaking macOS Firewalls |
| - | Follow the White Rabbit: Simplifying Fuzz Testing Using FuzzExMachina |
| - | For the Love of Money: Finding and Exploiting Vulnerabilities in Mobile Point of Sales Systems |
| - | From Bot to Robot: How Abilities and Law Change with Physicality |
| - | From Thousands of Hours to a Couple of Minutes: Automating Exploit Generation for Arbitrary Types of Kernel Vulnerabilities |
| - | From Workstation to Domain Admin: Why Secure Administration isn't Secure and How to Fix it |
| - | GOD MODE UNLOCKED - Hardware Backdoors in x86 CPUs |
| - | Hardening Hyper-V through Offensive Security Research |
| - | Holding on for Tonight: Addiction in InfoSec |
| - | How can Communities Move Forward After Incidents of Sexual Harassment or Assault? |
| - | How can Someone with Autism Specifically Enhance the Cyber Security Workforce? |
| - | How I Learned to Stop Worrying and Love the SBOM |
| - | I for One Welcome Our New Power Analysis Overlords |
| - | Identity Theft: Attacks on SSO Systems |
| - | InfoSec Philosophies for the Corrupt Economy |
| - | IoT Malware: Comprehensive Survey Analysis Framework and Case Studies |
| - | Is the Mafia Taking Over Cybercrime? |
| - | It's a PHP Unserialization Vulnerability Jim but Not as We Know It |
| - | KeenLab iOS Jailbreak Internals: Userland Read-Only Memory can be Dangerous |
| - | Kernel Mode Threats and Practical Defenses |
| - | Last Call for SATCOM Security |
| - | Legal Landmines: How Law and Policy are Rapidly Shaping Information Security |
| - | Legal Liability for IOT Cybersecurity Vulnerabilities |
| - | Lessons and Lulz: The 4th Annual Black Hat USA NOC Report |
| - | Lessons from Virginia - A Comparative Forensic Analysis of WinVote Voting Machines |
| - | Lowering the Bar: Deep Learning for Side Channel Analysis |
| - | LTE Network Automation Under Threat |
| - | Mainframe [z/OS] Reverse Engineering and Exploit Development |
| - | Measuring the Speed of the Red Queen's Race; Adaption and Evasion in Malware |
| - | Meltdown: Basics Details Consequences |
| - | Mental Health Hacks: Fighting Burnout Depression and Suicide in the Hacker Community |
| - | Miasm: Reverse Engineering Framework |
| - | Money-rity Report: Using Intelligence to Predict the Next Payment Card Fraud Victims |
| - | New Norms and Policies in Cyber-Diplomacy |
| - | New Trends in Browser Exploitation: Attacking Client-Side JIT Compilers |
| - | No Royal Road … Notes on Dangerous Game |
| - | None of My Pixel is Your Business: Active Watermarking Cancellation Against Video Streaming Service |
| - | Open Sesame: Picking Locks with Cortana |
| - | Outsmarting the Smart City |
| - | Over-the-Air: How we Remotely Compromised the Gateway BCM and Autopilot ECUs of Tesla Cars |
| - | Pestilential Protocol: How Unsecure HL7 Messages Threaten Patient Lives |
| - | Playback: A TLS 1.3 Story |
| - | Practical Web Cache Poisoning: Redefining 'Unexploitable' |
| - | Protecting the Protector Hardening Machine Learning Defenses Against Adversarial Attacks |
| - | Real Eyes Realize Real Lies: Beating Deception Technologies |
| - | Reconstruct the World from Vanished Shadow: Recovering Deleted VSS Snapshots |
| - | Remotely Attacking System Firmware |
| - | Return of Bleichenbacher's Oracle Threat (ROBOT) |
| - | Reversing a Japanese Wireless SD Card - From Zero to Code Execution |
| - | Screaming Channels: When Electromagnetic Side Channels Meet Radio Transceivers |
| - | SDL That Won't Break the Bank |
| - | SirenJack: Cracking a 'Secure' Emergency Warning Siren System |
| - | Snooping on Cellular Gateways and Their Critical Role in ICS |
| - | So I became a Domain Controller |
| - | Software Attacks on Hardware Wallets |
| - | Squeezing a Key through a Carry Bit |
| - | Stealth Mango and the Prevalence of Mobile Surveillanceware |
| - | Stop that Release There's a Vulnerability! |
| - | Stress and Hacking: Understanding Cognitive Stress in Tactical Cyber Ops |
| - | Subverting Sysmon: Application of a Formalized Security Product Evasion Methodology |
| - | The Air-Gap Jumpers |
| - | The Finest Penetration Testing Framework for Software-Defined Networks |
| - | The Problems and Promise of WebAssembly |
| - | The Science of Hiring and Retaining Female Cybersecurity Engineers |
| - | The Unbearable Lightness of BMC's |
| - | The Windows Notification Facility: Peeling the Onion of the Most Undocumented Kernel Attack Surface Yet |
| - | There will be Glitches: Extracting and Analyzing Automotive Firmware Efficiently |
| - | Threat Modeling in |
| - | TLBleed: When Protecting Your CPU Caches is Not Enough |
| - | TRITON: How it Disrupted Safety Systems and Changed the Threat Landscape of Industrial Control Systems Forever |
| - | Two-Factor Authentication Usable or Not? A Two-Phase Usability Study of the FIDO U |
| - | Understanding and Exploiting Implanted Medical Devices |
| - | Unpacking the Packed Unpacker: Reverse Engineering an Android Anti-Analysis Native Library |
| - | WebAssembly: A New World of Native Exploits on the Browser |
| - | Why so Spurious? How a Highly Error-Prone x86/x64 CPU Feature can be Abused to Achieve Local Privilege Escalation on Many Operating Systems |
| - | Windows Offender: Reverse Engineering Windows Defender's Antivirus Emulator |
| - | WireGuard: Next Generation Secure Network Tunnel |
| - | Wrangling with the Ghost: An Inside Story of Mitigating Speculative Execution Side Channel Vulnerabilities |
| - | Your Voice is My Passport |
| - | ZEROing Trust: Do Zero Trust Approaches Deliver Real Security? |
How to easy check?
https://www.blackhat.com/us-18/briefings.html 페이지에서..
data = document.getElementsByClassName('h2-link')
for (var i in data) {
console.log(data[i].title)
}
자바스크립트로 돌리면 편합니다. h2-link class가 각 발표 세션 제목이기 때문이죵